11 | Add to Reading ListSource URL: media.blackhat.comLanguage: English - Date: 2012-04-07 14:20:24
|
|---|
12 | Add to Reading ListSource URL: modi.mech.columbia.eduLanguage: English - Date: 2013-06-05 17:33:08
|
|---|
13 | Add to Reading ListSource URL: us.sourcesecurity.comLanguage: English - Date: 2012-07-10 09:02:34
|
|---|
14 | Add to Reading ListSource URL: www.biometricsinstitute.orgLanguage: English - Date: 2011-07-12 20:38:13
|
|---|
15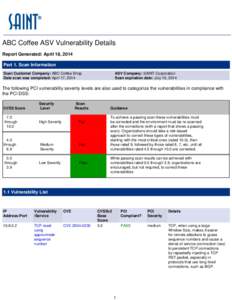 | Add to Reading ListSource URL: www.saintcorporation.comLanguage: English - Date: 2014-04-22 13:49:11
|
|---|
16 | Add to Reading ListSource URL: eprint.iacr.orgLanguage: English - Date: 2007-11-26 05:40:58
|
|---|
17 | Add to Reading ListSource URL: www.rs-computer.comLanguage: English - Date: 2009-12-15 09:43:31
|
|---|
18![A Note on the Relay Attacks on e-passports? The Case of Czech e-passports Martin Hlav´aˇc1 and Tom´aˇs Rosa1,2 [removed] and [removed] 1 A Note on the Relay Attacks on e-passports? The Case of Czech e-passports Martin Hlav´aˇc1 and Tom´aˇs Rosa1,2 [removed] and [removed] 1](https://www.pdfsearch.io/img/485d493d8252c4d000c7be027342fe5f.jpg) | Add to Reading ListSource URL: eprint.iacr.orgLanguage: English - Date: 2007-06-24 13:33:18
|
|---|
19 | Add to Reading ListSource URL: www.infosec.gov.hkLanguage: English - Date: 2013-01-28 04:23:20
|
|---|
20 | Add to Reading ListSource URL: www.infosec.gov.hkLanguage: English - Date: 2013-01-28 04:23:20
|
|---|